Oak View Group Names Industry Veteran Michele Powell as General Manager of Kansas Athletics Venue Operations
Oak View Group (OVG), the global leader in premium live entertainment infrastructure and services, today announced the appointment of industry veteran Michele Powell as General Manager for operations at the University of Kansas. In this role, Powell oversees OVG’s operations at Kansas, including venue management at David Booth Kansas Memorial Stadium and the new Naismith Club at Allen Fieldhouse.
(OVG), the global leader in premium live entertainment infrastructure and services, today announced the appointment of industry veteran Michele Powell as General Manager for operations at the University of Kansas. In this role, Powell oversees OVG’s operations at Kansas, including venue management at David Booth Kansas Memorial Stadium and the new Naismith Club at Allen Fieldhouse.
Powell leads Oak View Group’s local team in Lawrence, KS, in driving event development, optimizing venue operations, and enhancing the overall fan and guest experience. She will also play a key role in identifying new programming opportunities, attracting marquee events, and integrating hospitality offerings and premium experiences. Powell joins OVG from Haslam Sports Group, where she most recently served as Vice President of Stadium Operations & Event Development.
“Michele is a proven leader who understands how to bring venues to life in a way that resonates with fans, partners, and the community,” said Greg O’Dell, President of Venue Management, Oak View Group. “As we continue to expand our partnership with the University of Kansas, her experience across operations, booking, and hospitality will help us unlock new opportunities and deliver a more connected, year-round experience in Lawrence.”
“I’m excited to join the team at Kansas and get to work,” said Powell. “There’s a strong foundation here, and I’m focused on supporting the team, building strong partnerships, and making sure we’re delivering a consistent, high-quality experience across every event.”
At Haslam Sports Group, Powell served as Vice President of Stadium Operations & Event Development. In that capacity, she oversaw operations, event development, and hospitality programming at Huntington Bank Field and event development and management at ScottsMiracleGro Field, and Historic Crew Stadium. She was responsible for managing multi-million dollar operating and capital budgets, coordinating complex event calendars, and leading the execution of large-scale concerts, sporting events, and festivals, while also building out robust hospitality and special events businesses across the venues
Prior to her role at Haslam, she served as Senior Vice President and General Manager of Capital One Arena with Monumental Sports & Entertainment, where she led all core venue functions including booking, operations, guest services, security, event production, and box office. Under her leadership, the arena hosted more than 200 events annually and served as home to multiple professional sports franchises and premier events. Powell’s career also includes senior roles in event booking and marketing, with extensive experience negotiating and producing a wide range of live events, from major concerts and touring productions to NCAA championships and large-scale civic events.
In addition to her industry leadership, Powell serves as an adjunct faculty member at The George Washington University, where she has taught graduate-level coursework focused on sports and event facility management.
OVG’s ongoing partnership with the University of Kansas reflects a long-term commitment to enhancing the game day and year-round experience through integrated venue management, elevated food and beverage offerings, and new premium gathering spaces. Together, these efforts aim to position Kansas as a premier destination for sports, entertainment, and community engagement.
Welcome to Our Newest Members!

Please welcome our newest members who joined IAVM in March 2026. Thank you for being a part of the association! Also, let us get to know you better by participating in the I Am Venue Management series. Please visit here to share your story and photo.
Nathaniel Arner, Orange County Convention Center, Orlando, FL
Brett Asanin, Maple Leaf Sports & Entertainment, Toronto, ON, Canada
Michelle Au, Orange County Convention Center, Orlando, FL
Lanaea Bailey, Proctors Collaborative, Schenectady, NY
Elizabeth Beedenbender, Fluegel Alumni Center, US Naval Academy Alumni Association & Foundation, Annapolis, MD
Tylor Begay, Massachusetts Convention Center Authority, Boston, MA
Jennifer Bell, Premium Parking, New Orleans, LA
Karron Benjamin, Greater Columbus Convention Center – Legends Global, Columbus, OH
Blake Bialk, Series Seating, Miami, FL
Lydia Binnig, Greater Columbus Convention Center – Legends Global, Columbus, OH
Andrew Birklid, Arup, Seattle, WA
Keagan Brown, Columbus Crew, Columbus, OH
Adam Budelli, AXS, Los Angeles, CA
Ally Burch, Salt Palace Convention Center, Salt Lake City, UT
Peter Burke, Arup, Seattle, WA
Kailee Carroll, Orange County Convention Center, Orlando, FL
Geoff Cheong, Populous, Kansas City, MO
Sky Ciolino, Palm Springs Plaza Theatre, Palm Springs, CA
Annie Clark, Columbia Metropolitan Convention Center, Columbia, SC
Tammy Clevenger, Greater Columbus Convention Center – Legends Global, Columbus, OH
Greg Cole, Minneapolis Convention Center, Minneapolis, MN
Kasandra Cook, Greater Columbus Convention Center – Legends Global, Columbus, OH
Dina Cooper, ConventionSuite by NewGen Business Solutions, Scottsdale, AZ
Tessa Devey, Thanksgiving Point, Lehi, UT
Eli Dryer, Jacob K. Javits Convention Center, New York, NY
Desiree Everett, Oregon Convention Center, Portland, OR
Alan Farmer, Columbia Metropolitan Convention Center, Columbia, SC
Crystal Flippin, Dayton Live, Dayton, OH
Kameron Foster, Greenville Convention Center, Greenville, SC
Hannah Gallagher, Orange County Convention Center, Orlando, FL
Stephanie Gaspari, Jacob K. Javits Convention Center, New York, NY
Sabrina Gerratana, Orange County Convention Center, Orlando, FL
Lisa Gladman, Greater Columbus Convention Center – Legends Global, Columbus, OH
Juliana Gordon, Orange County Convention Center, Orlando, FL
Andrew Graham, Barclays Center, Brooklyn, NY
Becky Grider, Kentucky Performing Arts, Louisville, KY
Shelby Hackett, Orange County Convention Center, Orlando, FL
Justin Haffner, Barclays Center, Brooklyn, NY
Jenna Hampel, Broward County Convention Center, Fort Lauderdale, FL
William Harrison, Essity Professional Hygiene, Philadelphia, PA
Lathanial Heisey, Morris Performing Arts, South Bend, IN
Shawn Higgins, accesso ShoWare Center, Kent, WA
Justin Horwitz, Jacob K. Javits Convention Center, New York, NY
Amy Huggins, Greater Columbus Convention Center – Legends Global, Columbus, OH
Andrea Johnson, Sodexo Live!, Greenville, SC
Emalynn Johnson, Orange County Convention Center, Orlando, FL
Ice Johnson, Greenville Convention Center, Greenville, SC
Christian Juarez, Palm Springs Plaza Theatre, Palm Springs, CA
Scott Keeton, Greater Columbus Convention Center – Legends Global, Columbus, OH
Ryan Keller, EverBank Stadium & Daily’s Place, Jacksonville, FL
Kelsey Kercado, Sodexo Live!, Orlando, FL
David Kingsbury, Target Center, Minneapolis, MN
Jon Kingston, Delta Center, Salt Lake City, UT
Ting Han Kuah, University of Iowa, Iowa City, IA
Nila Kushner, Orange County Convention Center, Orlando, FL
Swaleha Lalani, TVS, Atlanta, GA
Cullen Lampman, Niagara Falls Convention Centre, Niagara Falls, ON, Canada
Darrell Leon, Lamar-Dixon Expo Center, Gonzales, LA
Lindsey Lightsey, Saban Center, Tuscaloosa, AL
Henry Logan, Greater Columbus Convention Center – Legends Global, Columbus, OH
Emily Lounsberry, Orange County Convention Center, Orlando, FL
Bryan Maciukiewicz, Essity Professional Hygiene, Philadelphia, PA
Monica Makins, Great Park Live, Irvine, CA
Amy Malin, Central Bank Center/Rupp Arena – OVG, Lexington, KY
Rob Mcconnaughey, Palm Springs Plaza Theatre, Palm Springs, CA
Sophie McGuire, Indiana Convention Center and Lucas Oil Stadium, Indianapolis, IN
Martha Mendel, Dolby Theatre, Hollywood, CA
Andrea Mokros, Hennepin Arts, Minneapolis, MN
Carlos Mora, Orange County Convention Center, Orlando, FL
Steve Moran, Greenville Convention Center, Greenville, SC
Elijah Newton, Orange County Convention Center, Orlando, FL
Natalie Nicholas, Lamar-Dixon Expo Center, Gonzales, LA
Leslie Nutter, Greater Columbus Convention Center – Legends Global, Columbus, OH
Michael O’Leary, OKC Fairgrounds, Oklahoma City, OK
Jerry Oliveira, Barclays Center, Brooklyn, NY
Bobby Olsen, NRG Park, Houston, TX
Patrick Padero, Essity Professional Hygiene, Philadelphia, PA
Keba Parker, Great Park Live, Irvine, CA
Cheryl Patterson, Greater Columbus Convention Center – Legends Global, Columbus, OH
Gracie Penland, Missouri State University, Mount Juliet, TN
Christopher Pepsnik, North Shore Center for the Performing Arts in Skokie, Skokie, IL
Chuck Price, Prevent Medical Solutions, Bloomington, CA
David Rees, Honda Center/ocV!BE, Anaheim, CA
Janice Reindl, Orange County Convention Center, Orlando, FL
Jordan Robinette, Greater Columbus Convention Center – Legends Global, Columbus, OH
Benjamin Rogers, Missouri State University, Carthage, MO
Jenn Rosenbaum, Boldyn Networks, Pompano Beach, FL
Lauren Roth, Jacob K. Javits Convention Center, New York, NY
Mike Saunders, Greater Columbus Convention Center – Legends Global, Columbus, OH
Abigail Sawyers, West Virginia University, Morgantown, WV
Nicholas Scachetti, Massachusetts Convention Center Authority, Boston, MA
Kyle Schmidt, Minneapolis Convention Center, Minneapolis, MN
Joe Shaw, Greater Columbus Convention Center – Legends Global, Columbus, OH
Esther Shepherd-Velarde, Great Park Live, Irvine, CA
Steph Shryock, North Shore Center for the Performing Arts in Skokie, Skokie, IL
Ericka Sokolower-Shain, Yerba Buena Center for the Arts, San Francisco, CA
Katie Spohr, Indiana University, Bloomington, IN
Joel Stein, Lamar-Dixon Expo Center, Gonzales, LA
Stefani Taylor, Segerstrom Center for the Arts, Costa Mesa, CA
Meghan Teves, Maple Leaf Sports & Entertainment, Toronto, ON, Canada
Jazz Traylor, Lamar-Dixon Expo Center, Gonzales, LA
Suzanne Turgeon, Greater Columbus Convention Center – Legends Global, Columbus, OH
Tony Turner, Barclays Center, Brooklyn, NY
Jordan Ullathorne, Massachusetts Convention Center Authority, Boston, MA
Steve VerDow, Greater Columbus Convention Center – Legends Global, Columbus, OH
Laura Wagner, Columbus Crew, Columbus, OH
Marciann Waters, Columbia Metropolitan Convention Center, Columbia, SC
Mia Watson, Xfinity Mobile Arena, Philadelphia, PA
Joshua Webb, College of Southern Nevada Performing Arts Center, North Las Vegas, NV
Gracie Weems, Niswonger Performing Arts Center, Greeneville, TN
Christopher Welch, Lamar-Dixon Expo Center, Gonzales, LA
Lea Westerfield, Greater Columbus Convention Center – Legends Global, Columbus, OH
Jason Wiatrak, Greater Columbus Convention Center – Legends Global, Columbus, OH
Janai Williams, Barclays Center, Brooklyn, NY
Michael Woolfenden, Essity Professional Hygiene, Philadelphia, PA
Anna Woolley, North Shore Center for the Performing Arts in Skokie, Skokie, IL
Jill Zingg, Branson Convention Center – Legends Global, Branson, MO
Long Beach Convention & Entertainment Center Completes $33 Million Infrastructure Overhaul, Turning Roof into City-Connected “Mini Solar Power Plant”
Landmark Sustainability Project Replaces Roof and HVAC Systems with 5,355 Solar Panels Generating Clean Energy for Long Beach and Surrounding Metros

Over 5,000 solar panels were installed as part of LCEC’s three-phase infrastructure and sustainability initiative. Photo courtesy LCEC
The Long Beach Convention & Entertainment Center (LBCEC), a City of Long Beach-owned venue, today announced the completion of a three-phase infrastructure and sustainability initiative totaling $33 million. The final phase, the installation of 5,355 solar panels across the venue’s roof, is now live, feeding clean energy directly into the public grid and establishing the LBCEC as one of the most energy-forward convention facilities on the West Coast.
The project unfolded across three stages beginning in Q3 2025 when over 566,000 square feet of roofing was replaced under a new Cool Roof System, improving the campus’s insulation, preventing leaks, and reducing the load-bearing weight of the structure by more than 707,000 pounds.

Thirty-two Air Handling Units (AHUs) were delivered and installed by helicopter. Photo credit: Jose Cordon, LBCEC
In December 2025, 32 Air Handling Units (AHUs) – the venue’s first HVAC replacement in 35 years – were delivered and installed by helicopter due to the scale and rooftop location of the equipment, delivering 952,320 cubic feet per minute of airflow capacity at 20–25% greater efficiency than the systems they replaced.
The third and final phase, now complete, sees the Convention Center and Terrace Theater rooftops covered in solar panels capable of generating an estimated 4.6 to 4.8 gigawatt-hours of electricity per year.
At full output, the solar installation is expected to generate enough electricity to power approximately 700 homes annually. The system feeds directly into the municipal grid, contributing to the City of Long Beach’s broader sustainability and carbon reduction commitments. Combined with the more efficient HVAC infrastructure, the venue anticipates a substantial reduction in overall energy consumption year over year.
“This $33 million infrastructure transformation at the Long Beach Convention & Entertainment Center demonstrates our city’s unwavering commitment to environmental leadership and fiscal responsibility,” said Mayor Rex Richardson. “By modernizing this iconic waterfront facility with cutting-edge HVAC systems and transforming our roof into a solar power plant, we’re not only reducing operational costs for taxpayers — we’re generating clean energy that powers hundreds of Long Beach homes. This project exemplifies how we can upgrade our public assets to serve today’s needs while building a more sustainable future for generations of Long Beach residents.”
“The Long Beach Convention & Entertainment Center has always been a cornerstone venue in our portfolio, and this infrastructure transformation reinforces our commitment to sustainable venue operations across North America,” said Josh Kritzler, president, North American venues & content for Legends Global, which manages the venue. “Projects like this demonstrate how our venues can partner with municipalities to modernize older facilities while simultaneously advancing environmental goals. The combination of energy-efficient systems and renewable energy generation sets a benchmark for the entire industry, proving that convention centers can be both operationally excellent and environmentally responsible.”
The LBCEC hosts hundreds of events annually, including the Long Beach Grand Prix, major conventions, and entertainment productions. As a city-owned facility, the center’s infrastructure improvements reflect a long-term commitment by the City of Long Beach to modernize its public assets, reduce operating costs, and invest in a more sustainable future for the community.
“This project represents a transformative moment for the Long Beach Convention & Entertainment Center. By replacing critical infrastructure that has served us for decades and adding a substantial solar installation, we’re not just modernizing the facility, we’re establishing a new operational standard for convention centers nationwide,” said Robert Smit, general manager of the LBCEC for Legends Global. “Guests will benefit from improved climate control and reliability, while the City of Long Beach gains a venue that actively contributes clean energy back to the community. It’s an investment that will pay dividends for generations.”
Raleigh Convention Center Announces New Director Of Events
 The Raleigh Convention Center, as part of the Raleigh Convention and Performing Arts Complex, is pleased to announce the promotion of Lori Shumpert to Director of Events.
The Raleigh Convention Center, as part of the Raleigh Convention and Performing Arts Complex, is pleased to announce the promotion of Lori Shumpert to Director of Events.
Shumpert joined the Raleigh Convention Center as an Event Manager in 2022 and was promoted to Senior Event Manager in 2025. She brings over 18 years of valuable experience spanning large-scale event management, premium services, and venue operations. Lori’s skill in managing complex events and leading teams, with a focus on mentoring and developing staff, elevates the Raleigh Convention Center’s commitment to exceptional client and guest experiences. This serves the Raleigh Convention Center well as it prepares to welcome a full schedule of guests in 2026 and move towards the coming expansion.
“Lori’s collaborative leadership and expertise are a major asset to this team. Her ability to think strategically paired with her meticulous attention to detail are invaluable for our mission to provide planners, attendees, and partners with a great experience” said Kerry Painter, Executive Director of The Complex.
Lori is an experienced leader in the event industry, having worked venues and organizations around the country before joining the Raleigh Convention Center in 2022. She is an active member of IAVM, having most recently served as the co-chair of the 2025 IAVM Super Regional in Raleigh. Lori will be attending and speaking at IAVM’s 2026 Super Regional conference this April.
“I’m excited to lead this great team of event professionals and to continue providing our clients with exceptional moments,” said Shumpert. “We’re constantly striving to reach new heights in customer satisfaction and operational excellence. I’m eager to keep this great momentum we have as our venue grows and we continue to offer more, bigger, and better space and moments for event planners.”
She began her new role on April 4.
Javits Center Launches ‘Javits on the Hudson’ Brand Campaign to Celebrate 40th Anniversary
 The Jacob K. Javits Convention Center has launched a new “Javits on the Hudson” brand campaign to commemorate its 40th anniversary. The campaign also marks one year since Joyce Leveston, CMM, CVP, became the convention center’s first female CEO.
The Jacob K. Javits Convention Center has launched a new “Javits on the Hudson” brand campaign to commemorate its 40th anniversary. The campaign also marks one year since Joyce Leveston, CMM, CVP, became the convention center’s first female CEO.
“This brand refresh is about showing the world who we are — a launchpad of innovation powered by some of the most talented and skilled workforce in the industry,” said Leveston.
Over 10% of the Javits Center team has been working at the venue for more than 20 years. “That kind of continuity speaks to something deeper than a workplace; it reflects a shared sense of purpose and pride in what Javits represents,” said Leveston. With this campaign, she said, “we’re bringing that story forward — placing our people at the center and ensuring that as we look ahead, we remain grounded in the values and spirit that have defined us for the past four decades.”

Photo courtesy of Javits Center
Javits Center’s history is one of progress, undergoing multiple renovations and expansions since opening its doors in 1986. With each update, the Center has increased its space and efficiency. It is LEED certified, outfitted with bird-friendly glass, topped by a nearly seven-acre green roof with solar panels and a one-acre rooftop farm. Joining the Net Zero Carbon Events Pledge in 2021 further cemented their reputation as a leader in sustainability.
“It was time to make sure the world knew what a center for inspiration Javits is on the global stage,” said Leveston.
After assembling her team — hiring the Center’s first ever director of marketing, along with a new Agency of Record (AOR) — Leveston got to work establishing her vision for the campaign.
“We wanted to make sure we are highlighting our best features like our waterfront location, our extensive sustainability initiatives, our relationship to our community and, of course, our people; all while holding on to our legacy as a New York icon,” said Leveston.
Javits on the Hudson
She described the colors chosen for the brand campaign as: Hudson Blue, representing Javits’ location on the waterfront; Farm Green, symbolizing their many sustainability initiatives; and Golden Yellow, complementing the signature trademark Javits Golden Apple.
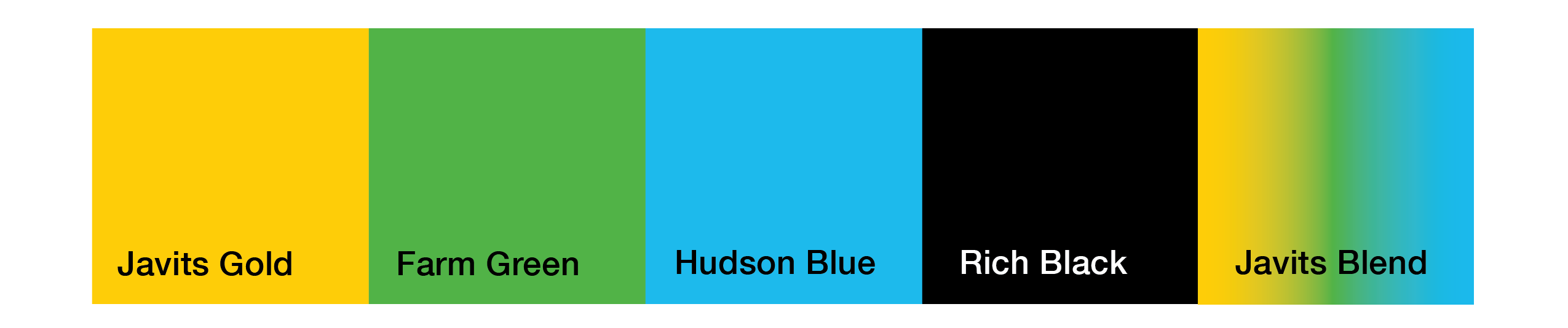
The branding also includes new graphic elements: a wave to represent the Hudson River, dots to mimic the pattern on Javits’ bird-friendly glass, forward-facing arrows to showcase the Center’s future mindset, and an NYC tag to honor their home city.

Leveston also explained that the Javits Center’s brand identity is led by four messaging pillars —
- A “Center for Inspiration” with a flexible campus that supports world-class events and experiences across industries.
- A place where “Connections Turn Into Movements” as gatherings spark new ideas, collaborations, and cultural moments are cemented.
- Fueled by “People-Powered Excellence” — a workforce and community that power the success of every event and experience.
- Where “Sustainability Meets Heart” as a national leader in sustainable operations, from the green roof habitat to energy and waste initiatives.
She emphasized that, “The golden apple remains at the heart of our brand because it represents the core of the Javits Center spirit.
“Javits Center has stood tall in support of New York for generations, both as an economic catalyst and as a community support system through defining moments like the Covid-19 pandemic and 9/11,” she said. “That spirit begins and endures with our people.”
Leveston’s First Year

Photo courtesy of Javits Center
More than anything, Leveston’s first year at the helm of Javits Center “has been an exercise in vision over execution.” This role required a change in perspective.
“My responsibility now is to define where we’re going, not just how we perform,” she said. “That means investing deeply in our people — through training, certifications, mentorship, and practicing emotional intelligence — so they are equipped to carry that vision forward.”
Looking back on the past year, she reflected on lessons learned: “Transformation isn’t just about strategy or design — it’s about people. When you invest in your team, trust their expertise, give them a voice, and bring them along with purpose and transparency, you don’t just refresh a brand — you strengthen the foundation for which it stands.”
She added, “What made this moment especially meaningful was that we weren’t building something new in a vacuum — we were shaping the next chapter of a 40-year legacy.”
Javits’ Next Chapter
In the coming year, the convention center will be introducing first-of-its-kind technology and becoming the first U.S. venue to introduce carbon insetting that will help them meet their ambitious Net-Zero Carbon Events Pledge.
As Leveston put it, “The future of Javits is about leadership — setting a higher standard for what our industry can be and delivering on it every day.”
Do you want to receive a Front Row News weekly digest?
Categories
- Allied (856)
- Architecture (147)
- Arenas (744)
- Career (890)
- Convention Centers (889)
- Education (608)
- Events (1,528)
- Food & Beverage (193)
- Foundation (113)
- Guest Experience (1,482)
- Industry News (2,253)
- Leadership (1,872)
- Marketing (150)
- Membership (1,985)
- Music (212)
- Performing Arts Centers (453)
- Professional Development (398)
- Research (127)
- Safety & Security (425)
- Sports (763)
- Stadiums (607)
- Student (159)
- Technology (515)
- Ticketing (92)
- Touring (82)
- Trends (357)
- Uncategorized (789)
- Universities (216)
- Video (25)
- Young Professional (198)
Twitter Feed
- Twitter feed loading
Recent Posts
- EIC Releases 2026 Global Economic Significance of Business Events Executive Summary
- City of Thomasville Awarded Multiyear Grant from Fox Gives
- Welcome to Our Newest Members
- Los Angeles Convention Center Partners with L.A. Neighborhood Land Trust to Beautify Local Communities with Native Wildflowers
- Connecting IAVM Volunteer Service With the Real World: How One IAVM Member Aligns Her Commitment at Work With the Value of Volunteering at the Regional Level
Categories
- Allied
- Architecture
- Arenas
- Career
- Convention Centers
- Education
- Events
- Food & Beverage
- Foundation
- Guest Experience
- Industry News
- Leadership
- Marketing
- Membership
- Music
- Performing Arts Centers
- Professional Development
- Research
- Safety & Security
- Sports
- Stadiums
- Student
- Technology
- Ticketing
- Touring
- Trends
- Uncategorized
- Universities
- Video
- Young Professional
Archives
- May 2026
- April 2026
- March 2026
- February 2026
- January 2026
- December 2025
- November 2025
- October 2025
- September 2025
- August 2025
- July 2025
- June 2025
- May 2025
- April 2025
- March 2025
- February 2025
- January 2025
- December 2024
- November 2024
- October 2024
- September 2024
- August 2024
- July 2024
- June 2024
- May 2024
- April 2024
- March 2024
- February 2024
- January 2024
- December 2023
- November 2023
- October 2023
- September 2023
- August 2023
- July 2023
- June 2023
- May 2023
- April 2023
- March 2023
- February 2023
- January 2023
- December 2022
- November 2022
- October 2022
- September 2022
- August 2022
- July 2022
- June 2022
- May 2022
- April 2022
- March 2022
- February 2022
- January 2022
- December 2021
- November 2021
- October 2021
- September 2021
- August 2021
- July 2021
- June 2021
- May 2021
- April 2021
- March 2021
- February 2021
- January 2021
- December 2020
- November 2020
- October 2020
- September 2020
- August 2020
- July 2020
- June 2020
- May 2020
- April 2020
- March 2020
- February 2020
- January 2020
- December 2019
- November 2019
- October 2019
- September 2019
- August 2019
- July 2019
- June 2019
- May 2019
- April 2019
- March 2019
- February 2019
- January 2019
- December 2018
- November 2018
- October 2018
- September 2018
- August 2018
- July 2018
- June 2018
- May 2018
- April 2018
- March 2018
- February 2018
- January 2018
- December 2017
- November 2017
- October 2017
- September 2017
- August 2017
- July 2017
- June 2017
- May 2017
- April 2017
- March 2017
- February 2017
- January 2017
- December 2016
- November 2016
- October 2016
- September 2016
- August 2016
- July 2016
- June 2016
- May 2016
- April 2016
- March 2016
- February 2016
- January 2016
- December 2015
- November 2015
- October 2015
- September 2015
- August 2015
- July 2015
- June 2015
- May 2015
- April 2015
- March 2015
- February 2015
- January 2015
- December 2014
- November 2014
- October 2014
- September 2014
- August 2014
- July 2014
- June 2014
- May 2014
- April 2014
- March 2014
- February 2014
- January 2014
- December 2013
- November 2013
- October 2013
- September 2013
- August 2013
- July 2013
- June 2013
- May 2013
- April 2013
- March 2013
- February 2013
- January 2013
- May 2012
- March 2012
- December 2011
- November 2011
- October 2011
Recent Comments
- Frank Bradshaw, Ph.D., CVE on John Meyer, CVE, a Tireless Advocate of Certification for Venue Professionals, Has Died
- Neil Sulkes on Hilary Hartung, Friend to Many in Venue Marketing, Has Left Us
- Jason Parker, CVE on The Devastation of Hurricane Helene and How We Can Support One Another
- Larry Perkins on Touhey Testifies Against Speculative Ticketing Before Congressional Subcommittee
- Peter Secord on Major Players for Planned Elkhart Amphitheater Were in the Mix at VenueConnect
